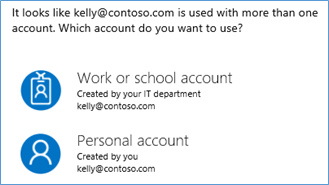
If you have a Microsoft Account (Live ID) username or alias that matches your Work or School Account (Azure AD) UPN, you will probably see a Home Realm Discovery prompt with annoying regularity. This is natural, and expected behaviour, but Microsoft has been taking steps to improve this experience, as detailed in their Cleaning up the #AzureAD and Microsoft account overlap article. Unsure if this is relevant to you? It is if you see this:
Interestingly, there is also now a link in some of these dialogue boxes which will prompt a user to resolve the issue by changing their conflicting Microsoft account username to some new alias. That prompt links to this support article. The basics of that process are:
- Add new alias
- Verify alias
- Make new alias primary
- Remove old alias
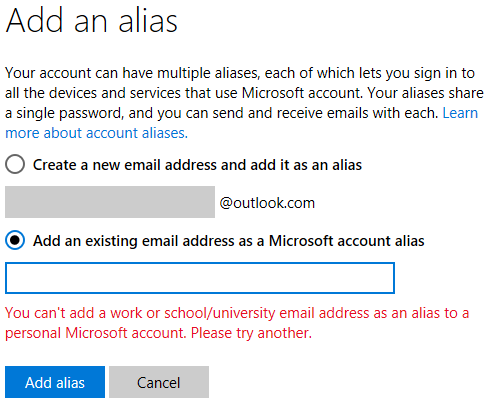
However, when I tried to make my new alias primary, the option was missing. I could only remove it. If I tried to remove the primary alias I was told to make the other alias primary first. Stuck! My colleague had five non-primary aliases, and just one of them was also missing this option. We tried a few things like signing on with the alias to see if that made a difference, but the option never appeared. Then, after a helpful suggestion from Oren Novotny I tried removing and adding the alias to see if that changed anything. Then, I couldn’t add it back at all. I would get this, “You can’t add a work or school/university email address as an alias to a personal Microsoft account. Please try another”, error:
This is precisely the restriction that Microsoft has put in place to prevent unnecessary Home Realm Discovery prompts, but we are unexpectedly seeing it when adding an alias. After a bit of testing, it appears that the restriction is scoped at the Azure AD Registered Domain Name. Organisations may register domain names with Azure AD either to prove ownership of a domain name for account creation, or for e-mail addresses/aliases. In my case (and my colleague’s), we added aliases to our Microsoft Accounts from registered domain names before Microsoft put this registered domain name restriction in place and we were trying to make these e-mail aliases our new primary Microsoft Account username after the restriction was introduced. The secondary issue here is that we hadn’t expected this restriction to take effect if the new alias didn’t in fact exist as an Azure AD username.
So… this all kind of makes sense once we put the pieces together, although it would be good if the Microsoft Account Manage How You Sign In to Microsoft page offered an explanation of why the alias cannot be made primary. This probably seems like the obscurest of issues, but I suspect many people will encounter it, since Microsoft are encouraging us to make a non-conflicting alias primary. The ultimate solution to this problem will require creation of a new alias in a namespace that hasn’t been registered with Azure AD.
You must be logged in to post a comment.